Bruno Security & Trust
Your APIs, Your Data | Always Local.
Bruno is built on a local-first, privacy-by-design model. We believe developers should have complete control over their data… no cloud syncs and no surprises.
Data Protection
Local-First Design
All your API collections, environments, and secrets are stored on your device.
Zero Cloud Storage
Bruno never sends or stores your data in the cloud.
Encryption
All connections (like license checks or updates) use TLS 1.2+ for secure communication.
How Bruno Works
Local Execution
Bruno runs 100% on your computer. Your files are stored as plain text, so you can manage them with Git, share them with your team, or keep them offline.
External Connections
Bruno performs an outbound call on app startup for the purposes of license key validation.
- Secure HTTPS request (port 443)
- Sends: IP address, license key, hashed device ID, and Bruno version
- No project data ever sent
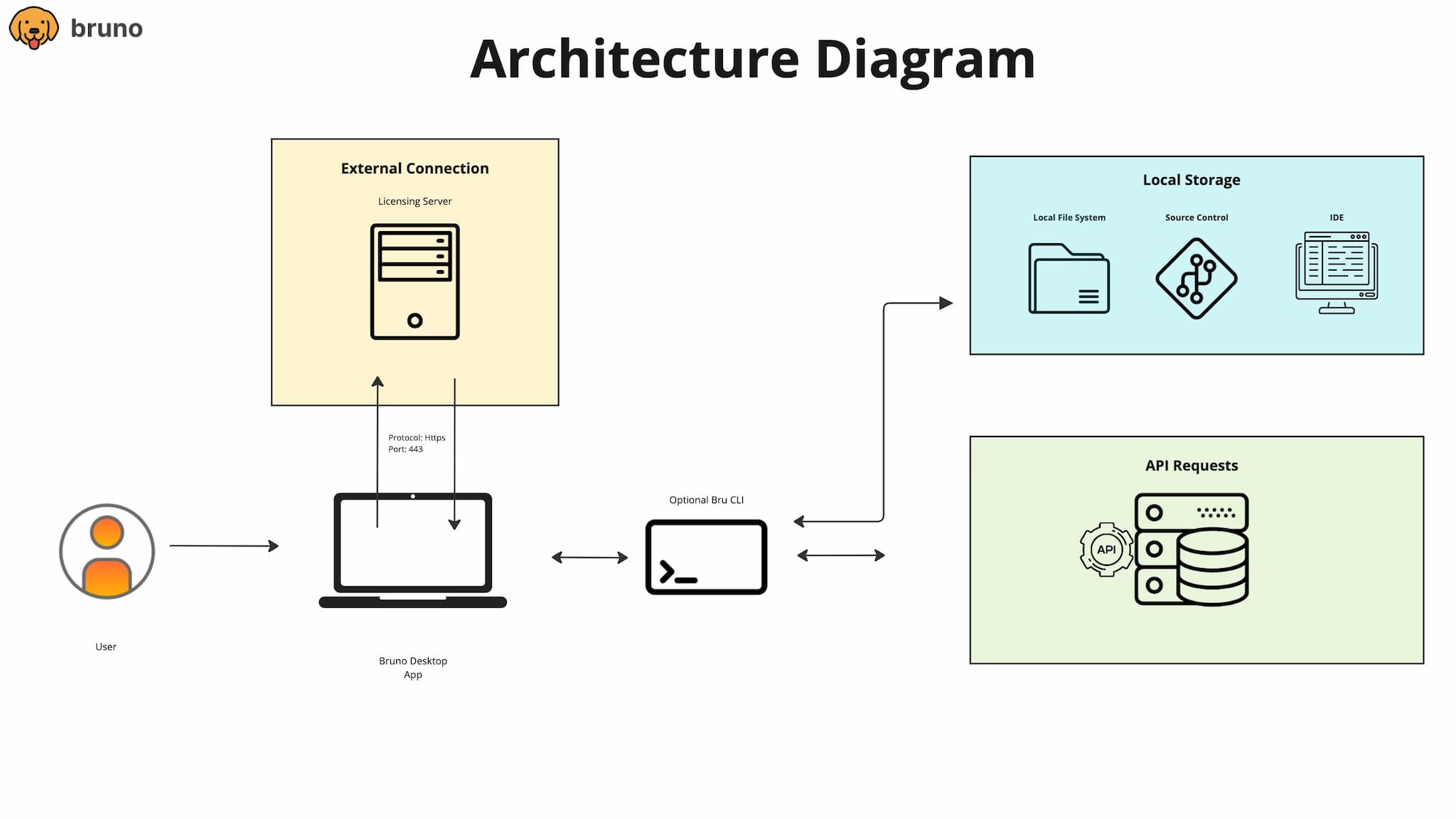
Architecture & Data Flow
Bruno's design is simple: everything runs locally, and data never leaves your environment.
Key Takeaways:
- Local-first storage and execution
- Outbound-only HTTPS call (port 443) for license validation
- No inbound connections or cloud sync
Network & Connectivity
Bruno operates with minimal, outbound-only connections — all over secure HTTPS (TLS 1.2+). No inbound ports are opened, and no user or project data ever leaves your environment.
All connections are outbound, encrypted, and limited to essential functionality. Bruno never opens inbound ports or transmits your API data.
| Purpose | Protocol | Port | Description |
|---|---|---|---|
| License verification | HTTPS | 443 | Securely validates your license key (encrypted; no API data transmitted). |
| API requests | HTTP / HTTPS | 80 / 443 | For your own API calls within Bruno. |
| App updates | HTTPS | 443 | To check for new Bruno versions (manual or automatic). |
Security Practices
Bruno follows strong internal security and development standards:
Access Control
Role-based access and multi-factor authentication for all internal systems.
Secure Development
Code reviews and dependency audits following OWASP principles.
Incident Response
Documented response plan for potential vulnerabilities or breaches.
Vendor Review
Third-party services undergo security checks and contractual data protection reviews.
Contact Our Security Team
If you have any questions, reach out to us at security@usebruno.com